
APPLE
Neal Mueller
Product
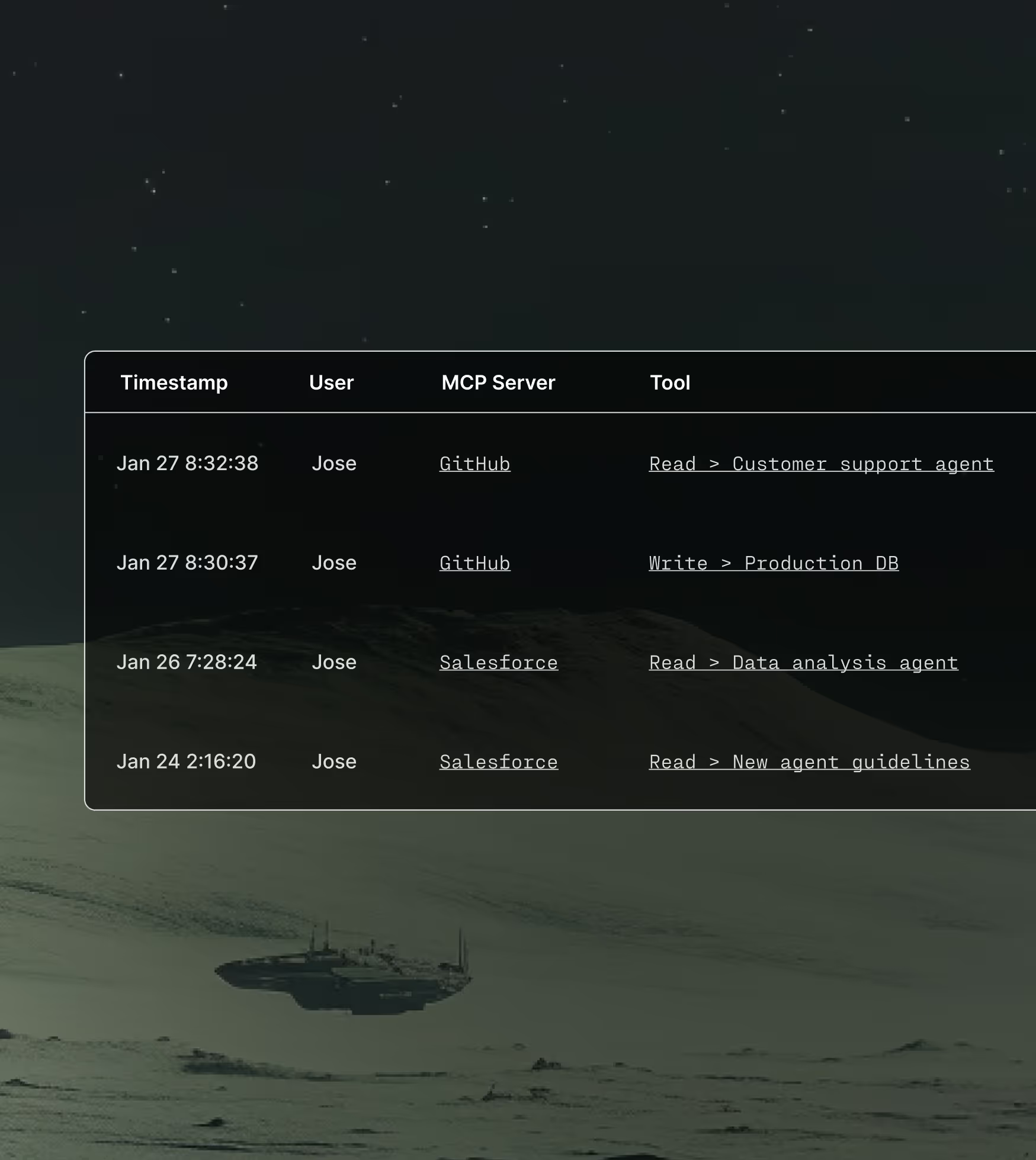
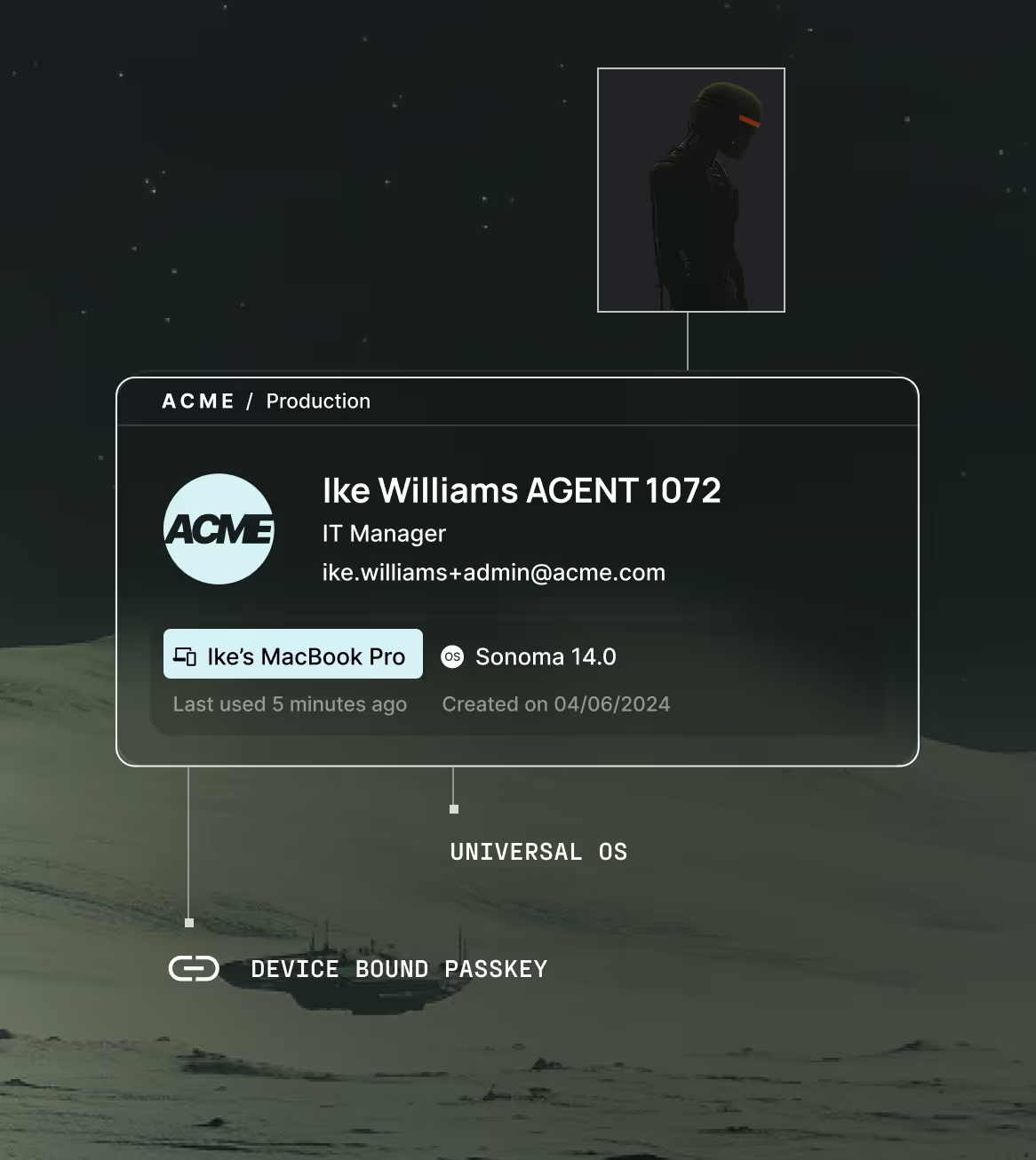
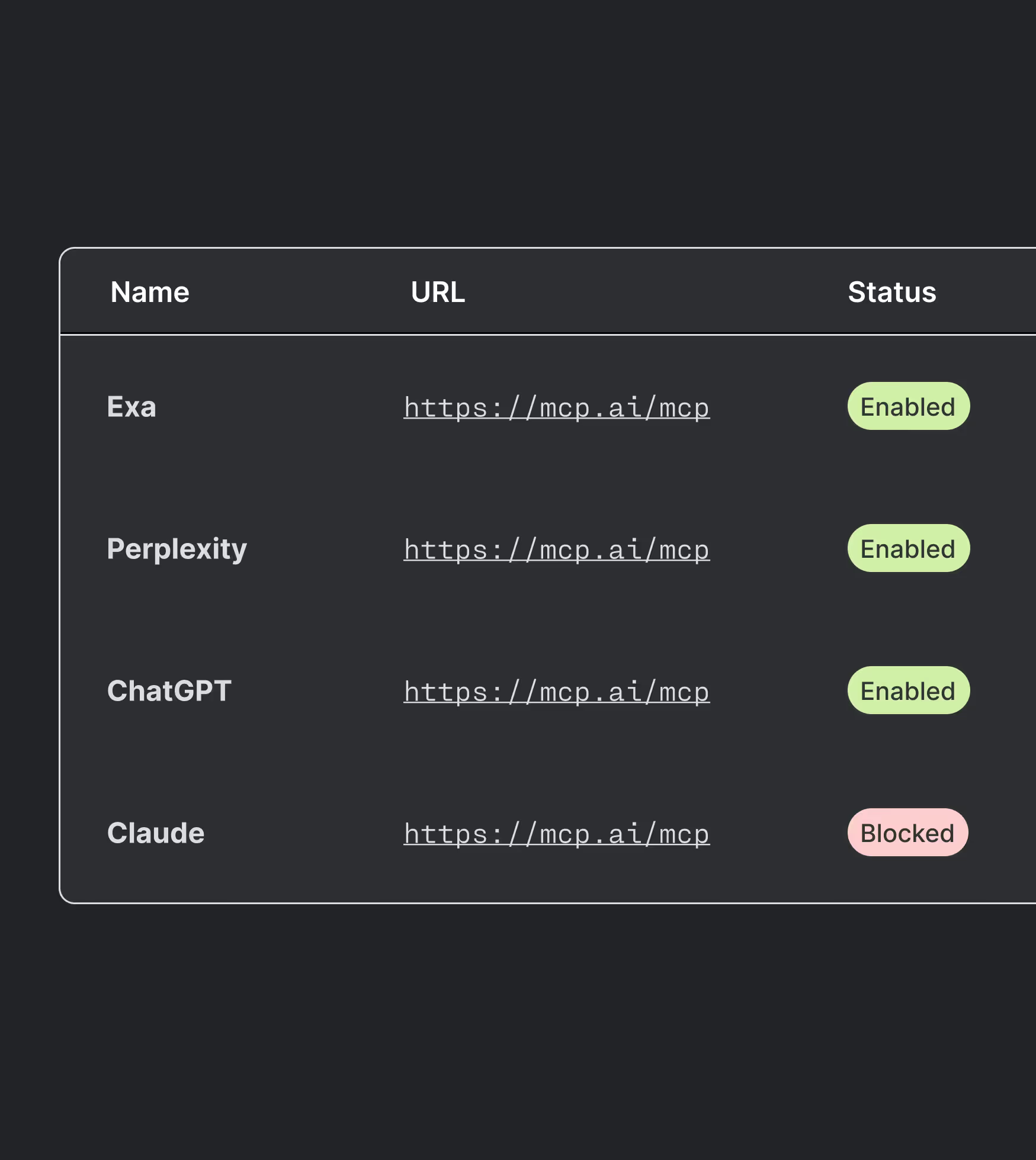
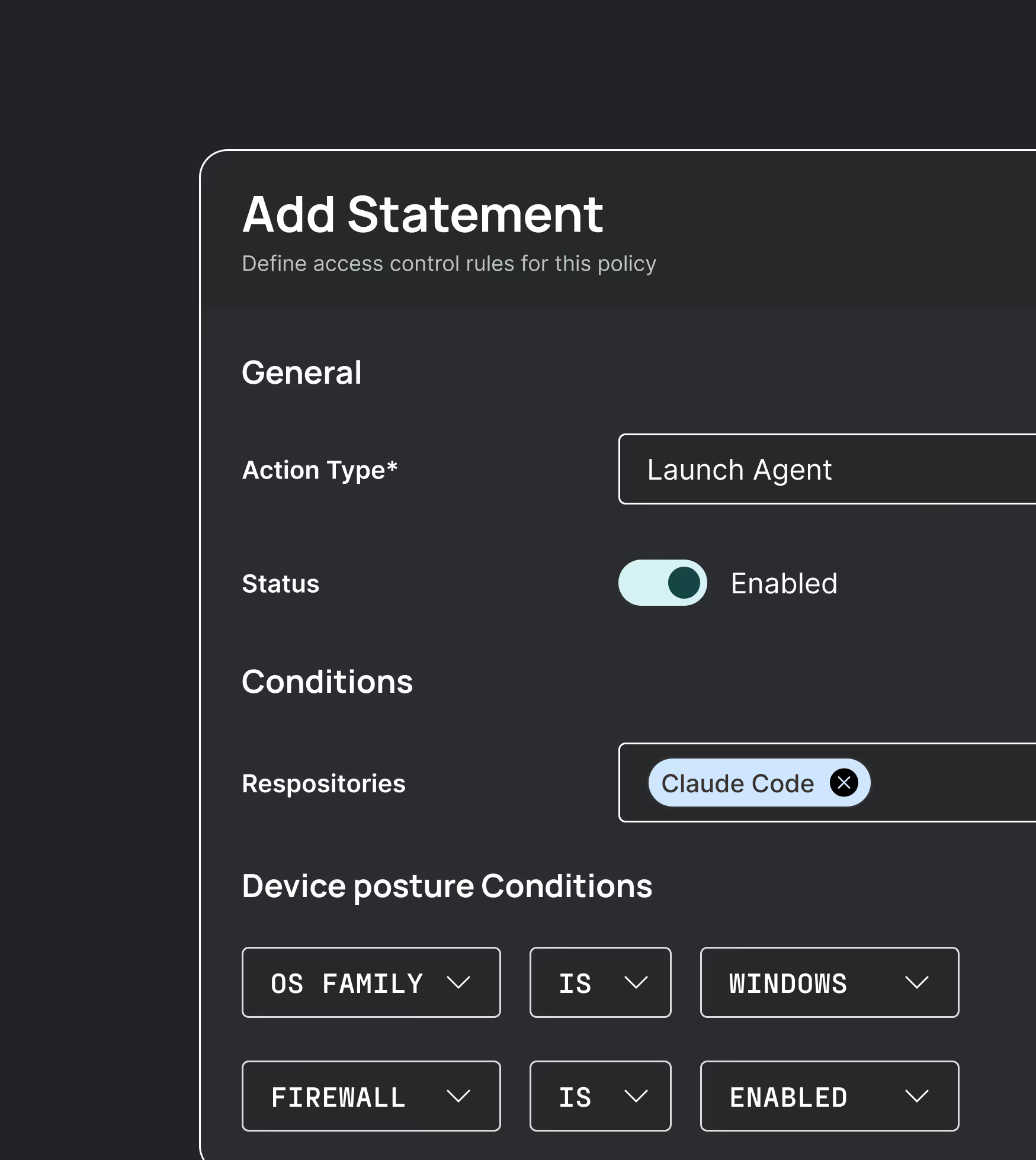
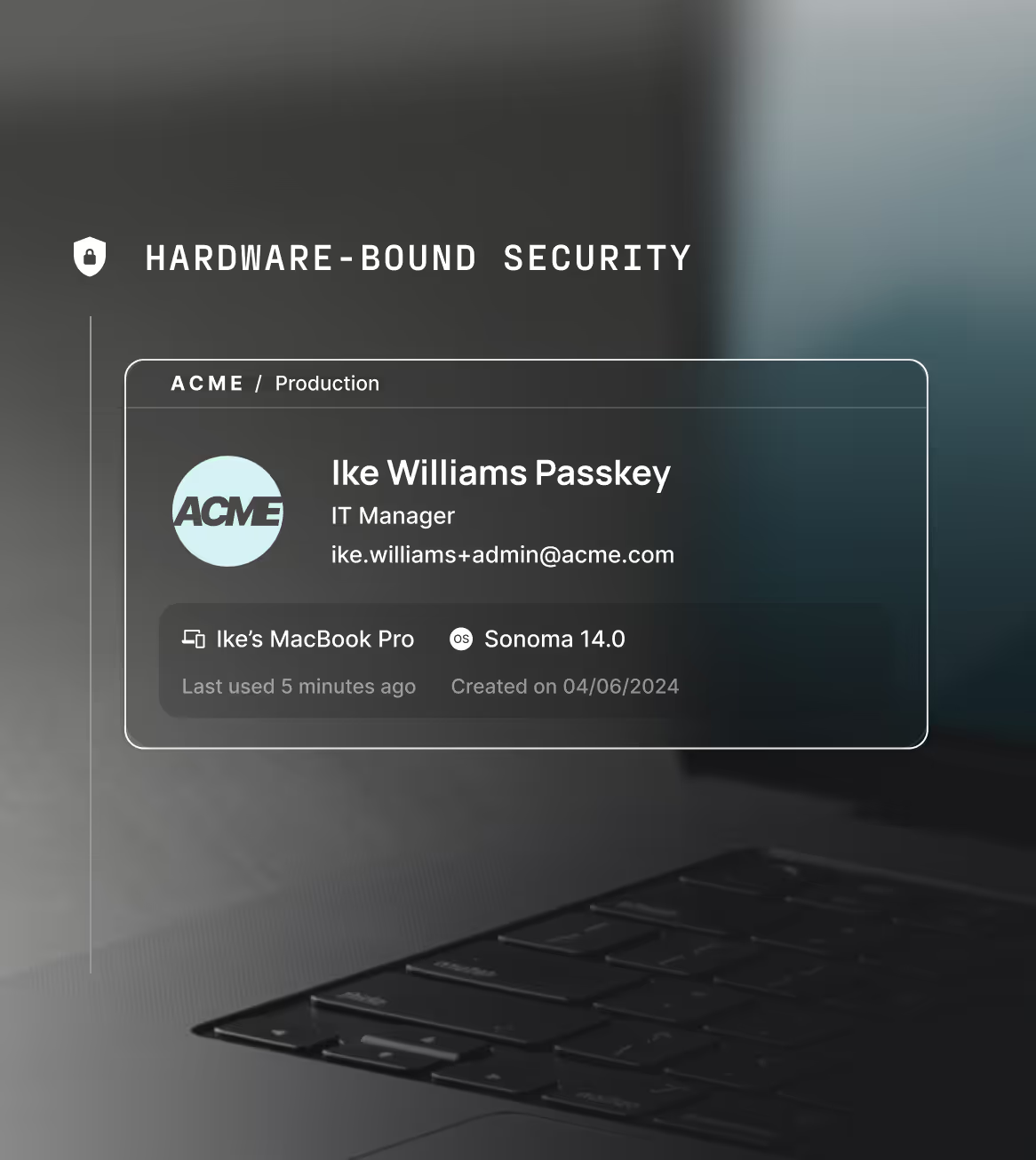
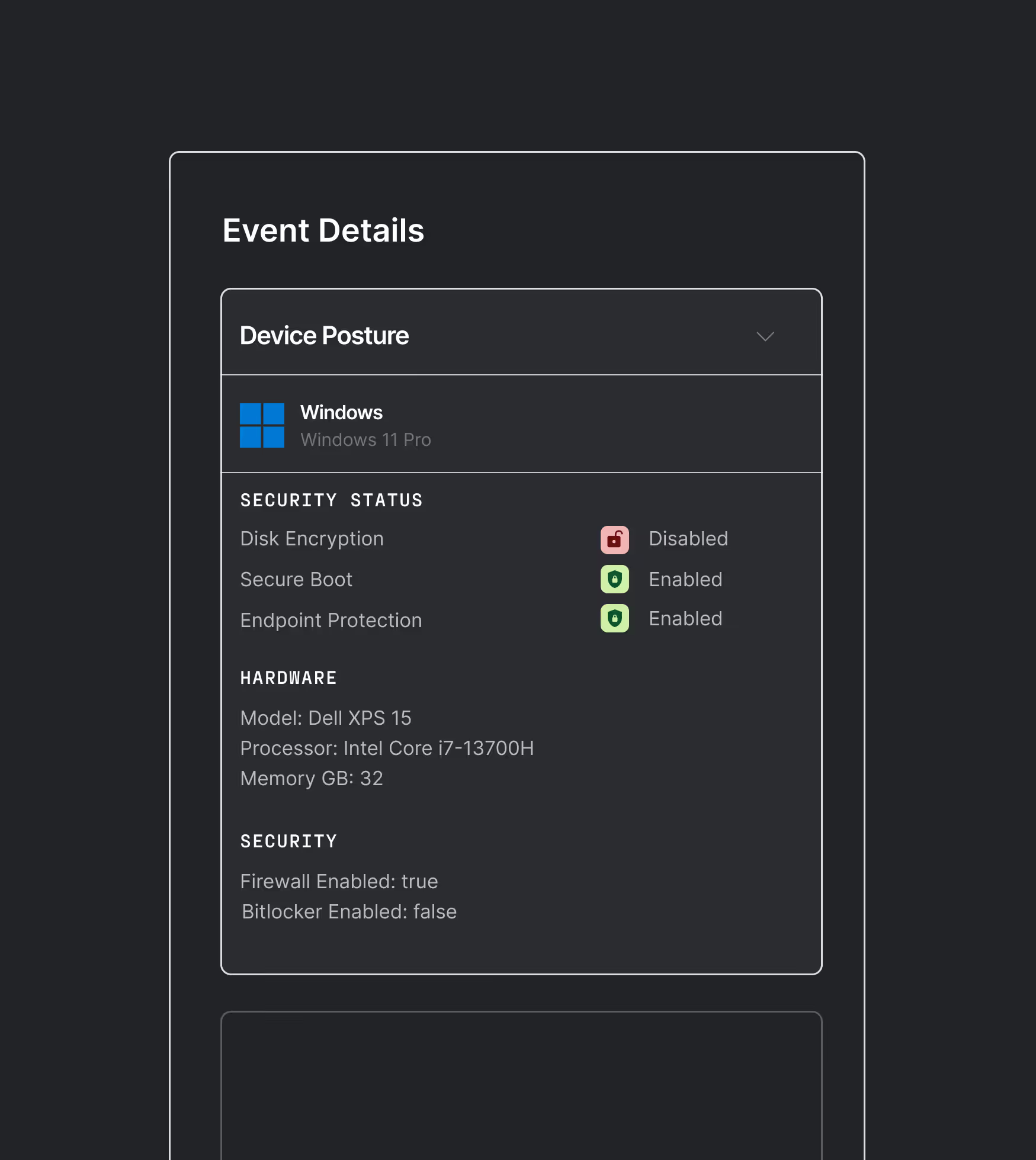
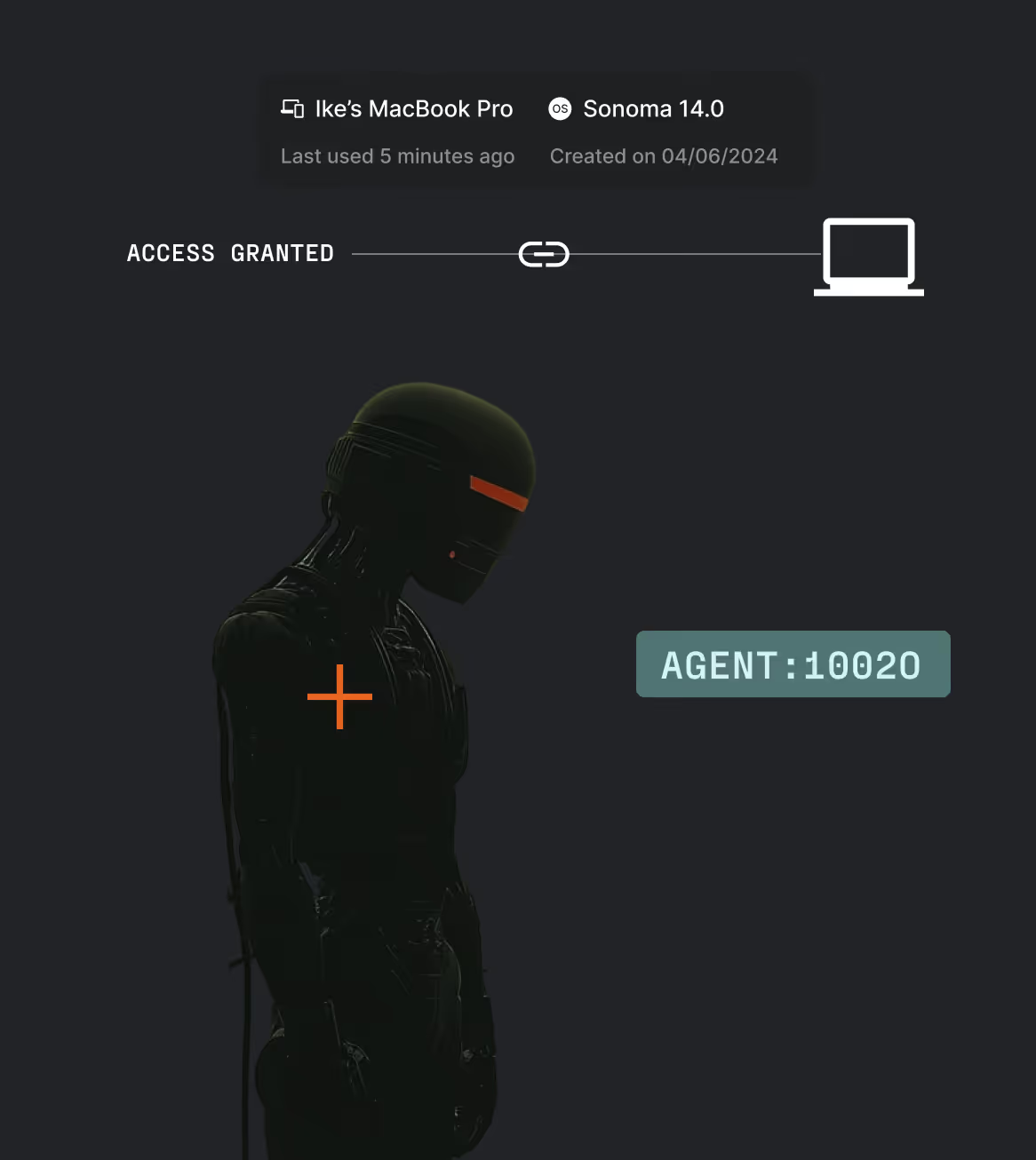
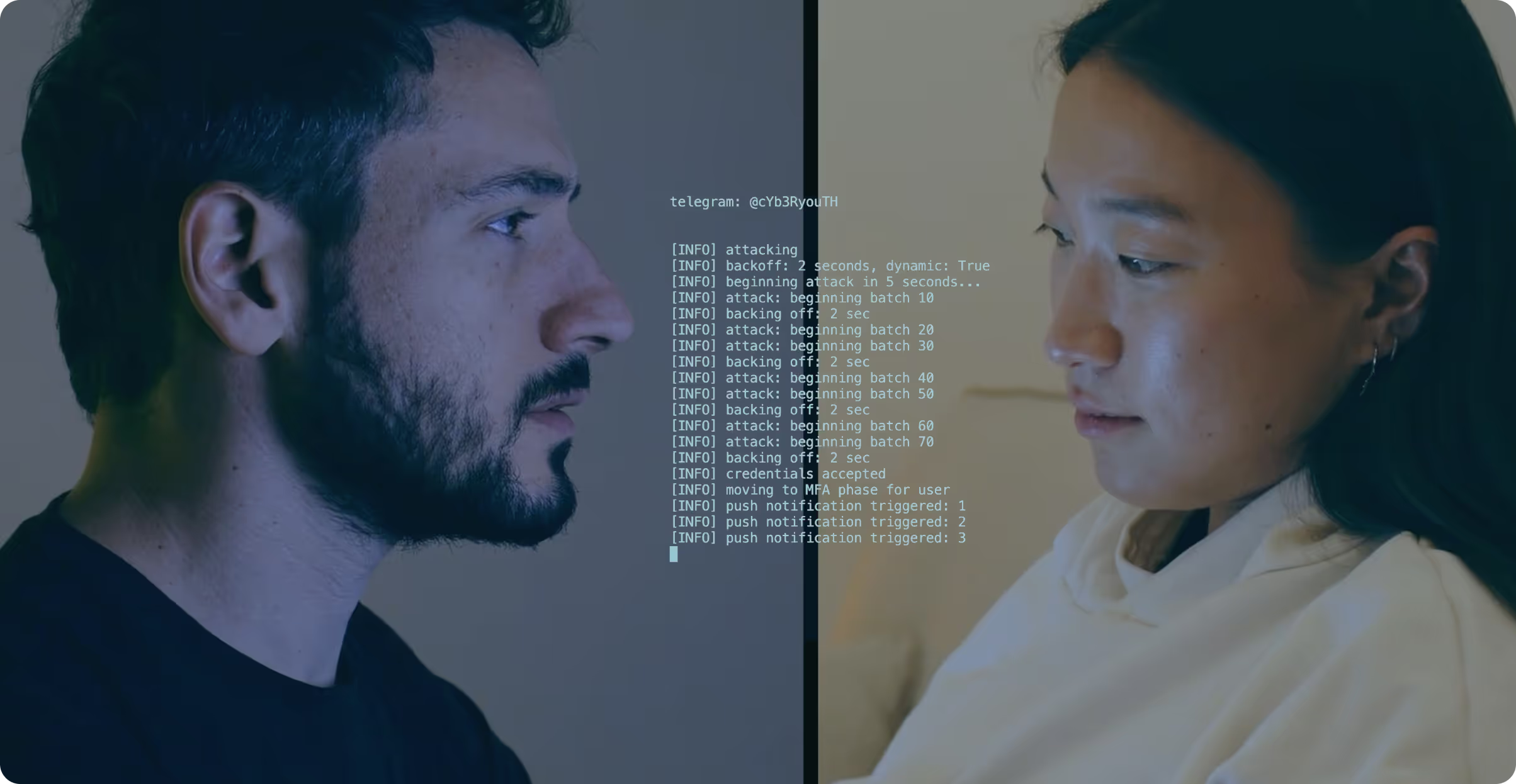
Ceros addresses agent security as a operational problem, not just a compliance checkbox. It monitors potential data exfiltration, enforce controls around sensitive tool and system access, and reduce real-world agentic engineering risks like prompt injection, over-permissioned workflows, and unintended actions across local and connected environments.




















.svg)





%20(1).avif)